The AI Shift in Cybersecurity
As traditional perimeters vanish, autonomous AI agents—Non-Human Entities—challenge existing security paradigms. Discover how Sidecar Agent Architecture redefines protection through SASE and ZTNA. Secure your infrastructure with "Dark Cloud" defenses and identity-centric authorization in this new "trust no one" era with the proposed 6W2Hows framework.
AI AGENTSCYBERSECURITY
Yiannis Bakopoulos assisted by Gemini AI
4/3/20263 min read
The AI Shift in Cybersecurity:
Realizing 'Dark Cloud' Security for Autonomous Agents.
In the contemporary technological landscape, the emergence of autonomous AI agents has necessitated a fundamental re-evaluation of cybersecurity paradigms. Traditional security perimeters are increasingly viewed as obsolete, given that agents possess the capability to operate within these perimeters, executing ostensibly legitimate tasks that may nonetheless cause systemic harm. Consequently, the dawn of this new era in cybersecurity is defined by the requirement to safeguard agents regardless of their physical or logical location. Within modern IT infrastructures, these autonomous agents are formally categorized as Non-Human Entities (NHEs).
NHE Identification and Credential Management
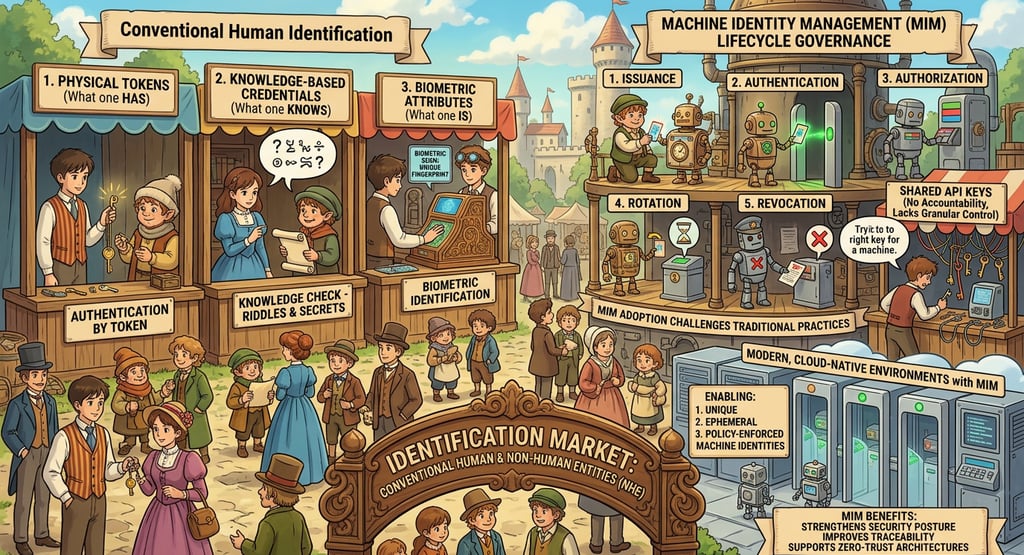
The identification of NHEs requires a sophisticated framework that diverges from traditional human authentication protocols. In contrast to conventional human identification mechanisms—such as physical tokens (what one has), knowledge-based credentials (what one knows), and biometric attributes (what one is) — Machine Identity Management (MIM) functions within a highly automated and distributed digital ecosystem where non-human entities require secure and scalable identity controls.
MIM governs the full lifecycle of machine credentials, including issuance, authentication, authorization, rotation, and revocation, across dynamic infrastructures. Its adoption challenges traditional cybersecurity practices that depend on shared API keys, which often lack accountability and granular control. By enabling unique, ephemeral, and policy-enforced machine identities, MIM strengthens security posture, improves traceability, and supports zero-trust architectures suited to modern, cloud-native environments.
Sidecar Agent Architecture
To enforce rigorous security guardrails, a Sidecar Agent Architecture is implemented. In this structural model, the primary agent must request access to data specifically through the sidecar proxy. The sidecar functions as a critical intermediary that receives requests, performs a comprehensive analysis to determine whether to accept or reject them based on established policies, and attaches the requisite credentials to execute the request on the agent's behalf.
This architecture facilitates several advanced security mechanisms:
Intent Inspection: While traditional firewall defenses rely on monitoring IP addresses and ports, the sidecar agent performs deep packet inspection of every request to ensure policy compliance and implement Data Loss Prevention (DLP) for Personally Identifiable Information (PII).
Micro-segmentation: This process establishes "digital bubbles" that designate approved operational paths, thereby restricting the agent's movement to authorized zones.
Behavioral Analytics: The sidecar agent continuously monitors agent activity for deviations from behavioral standards established by SASE policies. This includes the empirical measurement of action velocity and the enforcement of rate limiting.
Behavioral Analysis of Anomalous Patterns
Autonomous agents may operate within legitimate margins while still posing a potential threat to system stability. Security policies must be designed to identify and mitigate "strange" or anomalous behaviors, such as:
Privilege Escalation: Instances where an agent attempts to acquire permissions exceeding its original assignment.
Indirect Prompt Injection: Adversarial attempts to manipulate or trick the system.
Resource Exhaustion: Activities that deplete system resources to the point of failure.
The Convergence of SASE and ZTNA
The integration of Secure Access Service Edge (SASE) and Zero Trust Network Access (ZTNA) provides a holistic framework for agent security. SASE is a comprehensive architecture that unifies SD-WAN networking with cloud-delivered security services, effectively reducing complexity by consolidating disparate point products into a single management interface. Within this framework, ZTNA functions as the primary security mechanism, facilitating granular, identity-centric control over private applications.
ZTNA is underpinned by three core principles: explicit verification based on all available data points, enforcement of least-privilege access to minimize the "blast radius" of potential compromises, and an "assume breach" mentality that uses micro-segmentation to prevent lateral movement. By masking applications from the public internet—a concept known as a "Dark Cloud"—this architecture effectively shrinks the attack surface to near zero.
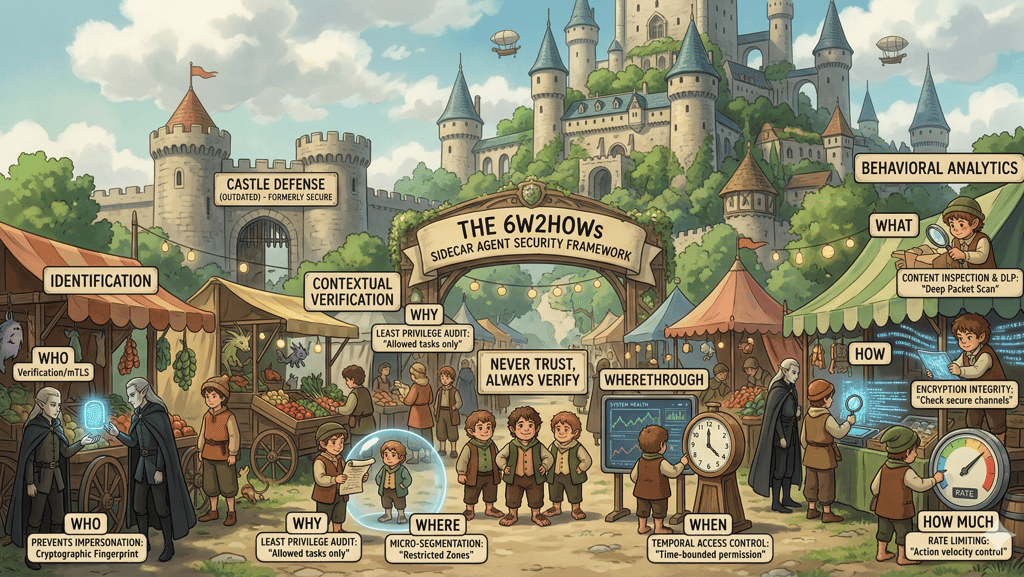
The 6W2Hows Policy Framework
The following checklist constitutes the proposed SASE policy for Sidecar Agents (AgentGuards) to ensure the rigorous safeguarding of all agent actions:
Conclusion
The paradigm of cybersecurity has undergone a definitive transition, moving away from the antiquated "castle-and-moat" architecture toward a contemporary "trust no one" philosophy. In this era of autonomous Non-Human Entities, the traditional security perimeter has effectively vanished, as agents can execute detrimental actions from within ostensibly secure environments.
Consequently, organizations must adopt SASE and ZTNA frameworks to enforce explicit verification across all operational vectors. By implementing the rigorous 6W2Hows checklist—encompassing Identity, Authorization, Micro-segmentation, Posture, Temporal constraints, Content, Integrity, and Rate Limiting—security administrators can maintain continuous, context-aware monitoring of agent behavior.
This shift necessitates shrinking the attack surface into a "Dark Cloud," rendering infrastructure invisible to unauthorized entities. Ultimately, safeguarding these autonomous agents requires replacing static IP-based defenses with persistent, identity-centric authorization.
Insights
Exploring AI's impact on people, society, and the environment.
Updates
Trends
ibakopoulos@aisociety.gr
Send email to...
This work is licensed under Creative Commons Attribution 4.0 International
